





































Project Background
Security can sometimes be like oxygen, easy to forget its presence until it is needed. However, by the time it is needed, it's most likely too late and has already caused irreparable damages. That is why even though security is not necessarily something particularly interesting to work on, it is still invariably crucial to many applications. Its importance is especially apparent in applications involving the government, military, or big corporations with a heavy emphasis on informational security. The need to transfer sensitive documents in physical copies is common for the situations mentioned above. Due to the special nature of the application, the deliverance process certainly can't be trusted by common delivery companies. It would not be a rare occasion for the organizations to form their delivery channels to ensure maximum security. Unfortunately, even with their delivery channels, the is always the threat of human error. With human nature being inherently prone to mistakes and corruptibility, blinding trusting people to accurately perform their job can be foolish and dangerous. An automated, self-verifying security system is needed to provide that extra layer of security.
Solution Details
As mentioned above, it's common for organizations that place a heavy emphasis on security to have their delivery channel. This eliminates some of the threats from the external world but offers no protection from internal perils. Adding more layers to the organization and more people to perform the job of verification on each other can help. However, it comes with the obvious downsides of extra cost, low efficiency, and the inability to counteract the threat of human error. An automated system can provide an economical and reliable alternative that removes some of the obscurity due to human psychology. With that being said, the system doesn't come without strings. It needs to be efficient to not slow the operation down. It also needs to have forms of countermeasure against malicious intent or human error, and the system needs to be easily traceable and transparent. Luckily, RFID comes to the rescue yet again.
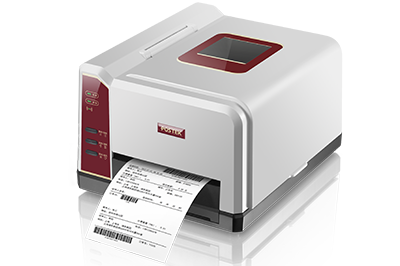
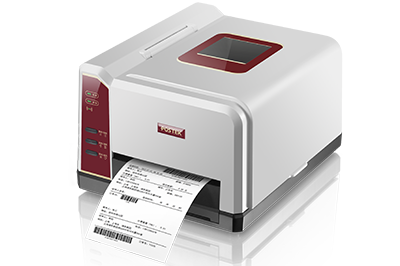
With POSTEK's RFID label printers integrated into the system, a corresponding RFID tag can be printed and applied to the file before it embarks on its journey. Relevant TID and detailed information about the file would be stored in the management software so the system is constantly aware of which unique RFID tag is associated with which file. With the RFID tag embedded inside the file, RFID antennas can be placed at all the key checkpoints through the file's journey and every detail about its delivery would be marked. Information such as which person took which file, when did the file get dropped off, how long a file has been stationary at a specific location, etc. All those important information regarding the file's journey not only offers clarity in the file's exact location at different points in time but also allows the system to respond to changes in real-time based on that information. Since the system knows exactly where the file should be at which time, files that have been stranded, or a person placed a file into the wrong compartment would trigger an alarm in the system and alert relevant personnel.
The inclusion of RFID into the system not only automates the tracking process but also gives the management software the necessary information to respond in real-time. With routes pre-planned for every file and up-to-date information on all files at all times, any deviation from the plan would be instantly detected. This early warning system allows for rapid deployment of countermeasures and ample time to prepare adequate responses. With the inclusion of POSTEK's G2000e RFID label printers, the requirement for on-demand RFID label printing/encoding can be met with ease. Equipped with TID feedback and RFID verification capabilities at the ready, the process of integrating the G2000e required minimal additional programming or maintenance for the system managers. Allowing for a seamless transition into their new upgraded security system.
Competitive Edge
1.High reliability and high portability. Equipped with many of POSTEK's innovative RFID features, the G2000e offers a smooth and reliable printing experience wherever it goes. The G2000e is also one that can get around. With the addition of an optional handle that allows for easy one-handed transportation, the G2000e is the perfect model for on-demand RIFD label printing.
2.Improved security. With the inclusion of RFID, the possibility of unauthorized personnel taking a wrong file without being noticed is eliminated. The entire course of the file's journey is also marked with time-stamped locations for easy traceability.
Automatic corrective measures. Since the system has full information over where the file should be at any given point in time, it can automatically utilize the tools available for a corrective effect. For example, if a file is stranded at a locker past its supposed pick-up time, the system can automatically alert the relevant personnel to the situation, providing them with the most amount of time possible to deal with the situation appropriately.